Windows 10, 8, 7 password recovery with Kali or ISeePassword
Recover Windows 10 administrator password with Kali Linux
Like Windows XP/7/8/8.1 passwords in Windows 10 are saved in SAM (Security Account Manager) file located in C:/Windows/system32/config. These password are encrypted with NTLMv2. This is how to dump the hashes and crack them using John password cracker tool:
Step 1:Boot Window machine with Kali Linux Live DVD/Flash Drive
Step 2: Mount Windows System Drive
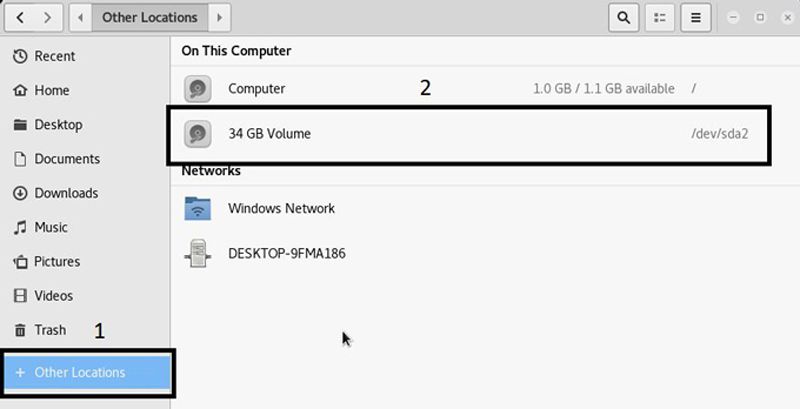
- Click on the Places and the menu bar will open click on Computer. The file manager will open.
- Click on other location, and again click on the Windows media. New windows will be open and looks like image.
Note: If you will not able to open this drive automatic use following command to fix error. This happen because Windows 10 does not shut down properly. By default it is going to sleep mode, So you will have to run following command.
#fdisk -l
this command is used to check the attached hardisk and its partition. its upto you how will you find the windows partition. if you will run following command with wrong partition, then no issue.
#ntfsfix /dev/sda2 (partition address)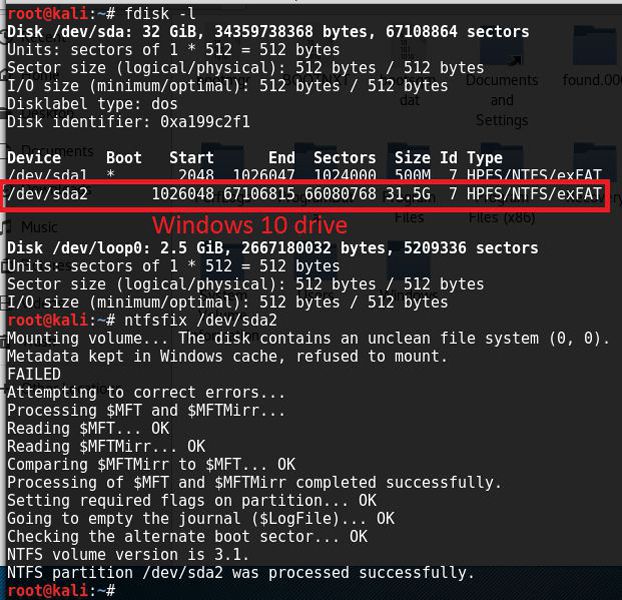
Try again to open Windows media, Once you will open go to next step.
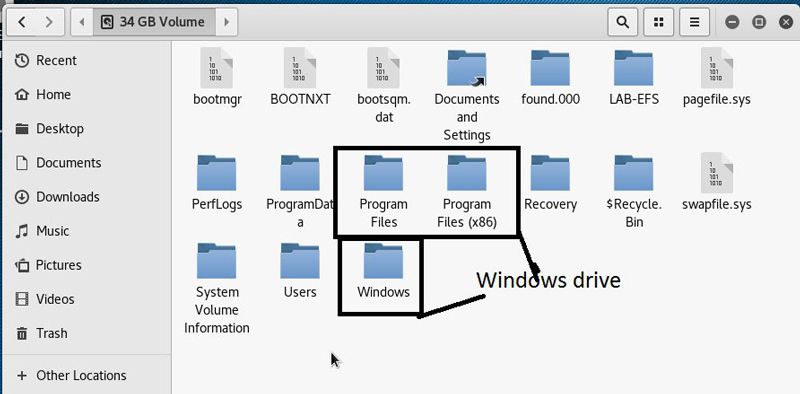
Step 3: Open terminal and Go into the SAM file location
#cd /Media/Media No./Windows/System32/config
Old method to get windows 10 password hashes
Step 4: Find the system bootkey using bkhive utility
#bkhive SYSTEM /root/Desktop/system
Step 5: Dump Password hashes using samdump2
#samdump2 SAM /root/Desktop/system > /root/Desktop/hashes.txt
New Method to get windows 10 password hashes – 2017
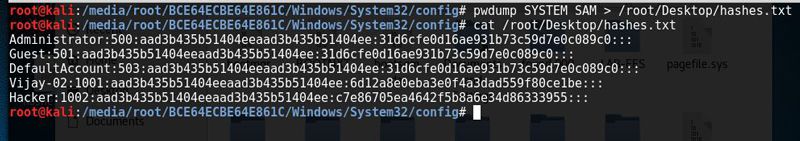
STEP 4+5: This is very important step, because in this step you are going to retrieve Windows 10 password hashes. So run the following command and dump the hashes.
#pwdump SYSTEM SAM > /root/Desktop/hashes.txt
You can provide any name instead of hashes.txt
(note: on Windows10 v1607 and later you might need pwdump8.exe — by Fulvio Zanetti and Andrea Petralia, supporting AES128 encrypted hashes)
I am only able to run pwdump8.exe from a Linux wine command as follows:
~/.wine$ wine "c:\pwdump8.exe" -f SYSTEM SAM
Step 6: Change working directory as /root/Desktop
#cd /root/Desktop
Step 7: See available hashes in hashes.txt file
#cat hashes.txt
Step 8: Find the password from hashes using John the Ripper
#john –format=nt2 –users=UserName hashes.txt 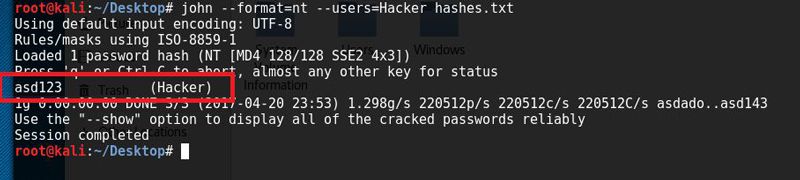
Find the password Have a fun
Recover Windows 10 administrator with iSeePassword ($29)
The tool iSeePassword Windows Password Recovery Pro, is a professional password recovery tool that is meant to reset or unlock a computer password. It is available for many Windows operating systems including Windows 10,8, 7 and XP. You will need a USB flash drive. When compared to other methods mentioned above, this is the easiest way to recover a lost password. It works by listing all user accounts on your computer, select a user account, and click the password reset button. You can login to your Windows account after restarting.
iSeePassword Windows Password Recovery Pro Steps
Step 1. Download iSeePassword Windows Password Recovery Pro and install and launch it on another available PC. There are two ways to burn a password reset disk, USB or DVD/CD, just inset a USB flash drive into it. Click “Burn”.
Step 2. When successful message pops up, click OK and exit removal device. Password recovery disk have been burned successfully.
Step 3: Insert the newly created USB drive to the locked Windows 10 computer. Set USB drive as the first boot device in BIOS setup. This computer will reboot. Then it will load the program, and detect all system and account on your computer, follow the interface to reset your Windows 10 password.
After you successfully reset the password, disconnect the boot disk and reboot your PC when password is reset to blank. Then your PC will restart normally and Windows 10 can login without password.
iSeePassword Windows Password Recovery Pro is easy to use and safe. With it,you can fast access to your windows if you forgot login password on Windows 10 without system re-installation.
