End of Service And Legacy of the Mormon Battalion
from California Pioneer Heritage Foundation Phone: 435-215-1417 or 530-308-3036 Email: cphf1@sbcglobal.net
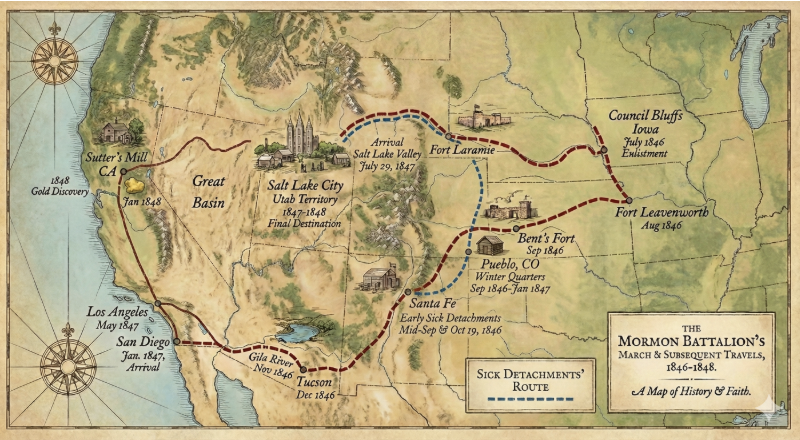
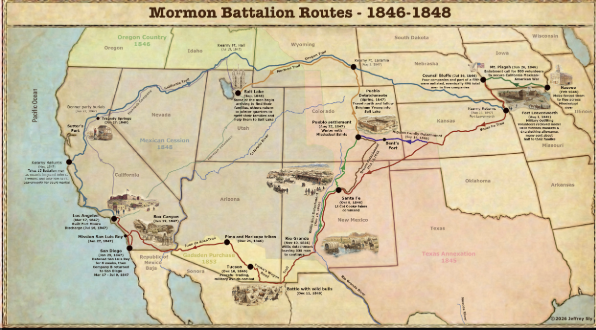
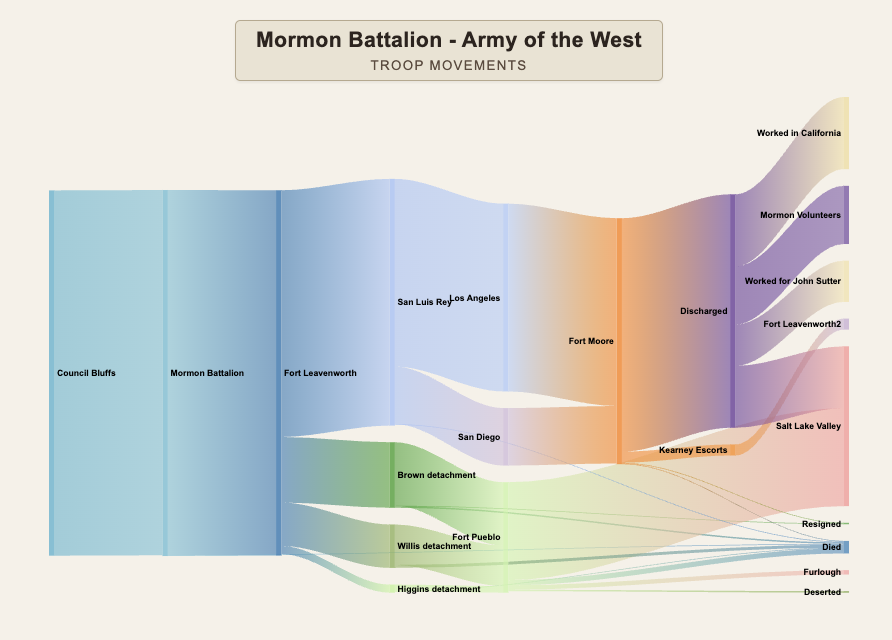
One of the main purposes of the Mormon Battalion was to provide Gen. Stephen Watts Kearny, Army of the West, with vital military manpower to back his assignment as military governor of Alta California. Kearny determined to employ his assets: The Mormon Battalion, 1st Dragoons, and 1st New York Volunteers (arrived by ship at Monterey, CA) to garrison duty at various key locations from San Diego to Los Angeles to put down any potential Mexican-Californio revolts to American occupation.